What are HID attacks?
👈HID attacks are a type of cyber attack that uses small flash-like devices to carry out hidden attacks on devices. These devices can copy passwords and sensitive information from your device, open a "back door" that allows a hacker to enter at will, and automatically execute complex commands within seconds on your device.
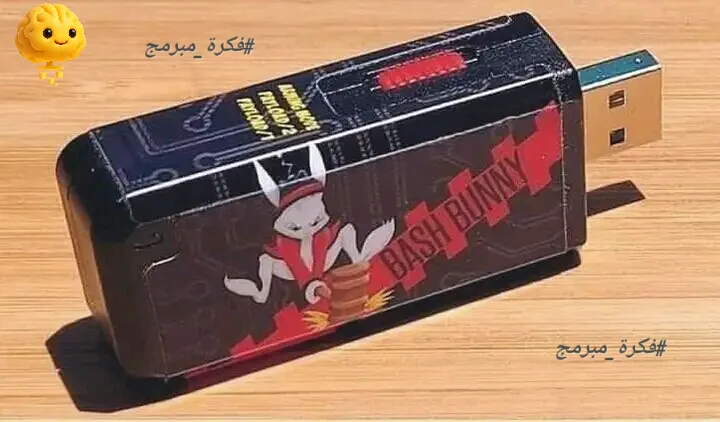
☝️Bash Bunny Tool: A complete hacking device
Bash Bunny is one of those devices that looks like a regular flash drive, but is actually a full-fledged hacking device. They can carry out stealth attacks on devices, copy passwords and sensitive information, and open a “back door” that allows a hacker to enter at will.
✌️ Regular flash programming
A regular flash drive can be programmed to perform almost the same function, making these attacks even more dangerous.
👌Device protection
- Avoid using unknown flash drives.
- Use protection and virus detection programs.
- Update your operating system and software regularly.
- Use strong and variable passwords.
👏Cyber awareness
You should be careful when using devices and flashes, and not trust anything that looks familiar. You should be aware of cyber threats and how to protect yourself from them.
#Network_Tips #Programmer_Idea #Ethical_Hacking #Technology_Explanation #Electronics_Basics #Cyber_Security