Iranian Cyber Attacks in 2026: Hacker Groups, Strategies, and Global Cyber Warfare
Iranian Cyber Attacks in 2026: Hacker Groups, Strategies, and Global Cyber Warfare
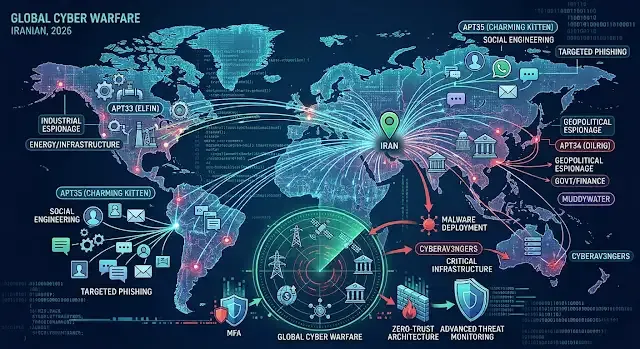
Cyber warfare has become one of the most powerful tools in modern geopolitics. Over the past decade, Iranian cyber attacks have evolved from small-scale hacking operations into sophisticated campaigns targeting governments, corporations, and critical infrastructure worldwide.
Today, Iran is considered one of the most active nation-state cyber actors, alongside Russia, China, and North Korea. These cyber operations involve espionage, sabotage, and digital influence campaigns that affect global security and technology ecosystems.
The Rise of Iran's Cyber Warfare Capabilities
Iran significantly accelerated its cyber capabilities after several cyber incidents targeted its national infrastructure in the early 2010s. Since then, the country has invested heavily in developing cyber units connected to intelligence and military organizations.
Two major institutions are believed to coordinate many cyber operations:
- Islamic Revolutionary Guard Corps (IRGC)
- Ministry of Intelligence and Security (MOIS)
These organizations reportedly support multiple hacker groups responsible for global cyber espionage campaigns and digital sabotage operations.
Major Iranian Hacker Groups (APT Actors)
Cybersecurity researchers have identified several Advanced Persistent Threat (APT) groups linked to Iranian cyber operations.
APT33 (Elfin)
APT33 focuses on industrial espionage and infrastructure attacks.
Primary targets include:
- Aviation companies
- Energy infrastructure
- Manufacturing organizations
- Defense contractors
The group frequently uses spear-phishing campaigns and password-spraying techniques to infiltrate corporate networks.
APT34 (OilRig)
APT34 is one of the most widely recognized Iranian cyber espionage groups.
Key characteristics:
- Active since 2014
- Targets government agencies and financial institutions
- Uses custom malware and credential-harvesting attacks
Their campaigns primarily focus on long-term intelligence gathering.
APT35 (Charming Kitten)
APT35 specializes in social engineering and targeted phishing operations.
Common targets include:
- Journalists
- Academic researchers
- Government officials
- Technology companies
The group frequently impersonates trusted contacts to trick victims into revealing login credentials.
Common Techniques Used in Iranian Cyber Attacks
Iranian cyber actors typically combine several hacking techniques to compromise systems and steal sensitive data.
Spear-Phishing Attacks
Highly targeted emails designed to trick victims into downloading malware or entering login credentials.
Credential Harvesting
Attackers create fake login pages to capture usernames and passwords.
Malware Deployment
Custom malware enables attackers to maintain long-term access to compromised networks.
Data Exfiltration
Sensitive data is stolen and sometimes leaked publicly as part of political pressure campaigns.
Distributed Denial-of-Service (DDoS)
Large botnets overwhelm servers, shutting down websites or disrupting online services.
Key Targets of Iranian Cyber Campaigns
Iranian cyber operations typically focus on sectors that hold strategic or geopolitical value.
Common targets include:
- Government institutions
- Energy and oil infrastructure
- Financial institutions
- Telecommunications companies
- Healthcare organizations
- Defense contractors
Critical infrastructure networks are particularly attractive targets because they can disrupt national economies and public services.
Why Iranian Cyber Attacks Matter
Although Iran's cyber capabilities are generally considered less advanced than those of China or Russia, the country has demonstrated an ability to conduct persistent and disruptive cyber campaigns.
Cyber warfare provides several strategic advantages:
- Lower cost compared to traditional warfare
- Ability to operate anonymously
- Potential to cause major disruption without military conflict
As geopolitical tensions increase, cyber operations have become a central component of modern state power.
How Organizations Can Defend Against State-Sponsored Cyber Attacks
Security experts recommend several defensive strategies to protect against sophisticated cyber threats.
1. Multi-Factor Authentication (MFA)
Adding additional authentication layers reduces the risk of credential theft.
2. Employee Cybersecurity Training
Many cyber attacks begin with phishing emails targeting employees.
3. Regular Security Updates
Patching vulnerabilities helps prevent attackers from exploiting outdated software.
4. Advanced Threat Monitoring
Security teams should implement SIEM and threat-intelligence platforms.
5. Zero-Trust Architecture
Every user and device must be verified before accessing sensitive systems.
The Future of Cyber Warfare
Cyber warfare is expected to become even more sophisticated as artificial intelligence and automation are integrated into offensive cyber operations.
Nation-states will continue to invest heavily in cyber capabilities to gain strategic advantages in the digital battlefield.
Understanding how Iranian cyber attacks operate is essential for governments, corporations, and cybersecurity professionals seeking to defend against modern cyber threats.
In the digital age, future conflicts may begin not with missiles or tanks — but with lines of code.
FAQ
What are Iranian cyber attacks?
Iranian cyber attacks are hacking operations conducted by groups linked to the Iranian government targeting governments, companies, and infrastructure for espionage or disruption.
Which hacker groups are linked to Iran?
Some of the most well-known groups include APT33, APT34, APT35, MuddyWater, and CyberAv3ngers.
What industries do Iranian hackers target?
Common targets include energy, government agencies, financial institutions, telecommunications, healthcare, and defense sectors.
How can organizations defend against these attacks?
Organizations should implement Zero-Trust security models, MFA authentication, threat monitoring, and employee cybersecurity training.