Cybersecurity - Understanding pirated software and “kits”: What should you know to protect yourself🤔?
👈In the world of hacking and cybersecurity, beginners ask a frequently asked question: How can hackers “break” a paid program like Microsoft Word without having the source code?
Today, the idea of a programmer explains it to you simply, with clear examples, and important warnings to protect your devices and data.
☝️ What is pirated software?
Pirate software is a modified version of paid software that has been manipulated to remove or bypass the license verification system so that it is illegally free.
✌️ How are programs broken without the source code?
Important question! These are the general steps:
- Reverse Engineering
Hackers do not have the original code, but they do have the executable file (.exe), which contains instructions that the computer understands.
Using tools like IDA Pro, Ghidra, and OllyDbg, they convert those instructions into a more understandable language (assembly language).
A simple analogy: You have a cake ready... you don't have the recipe, but you are trying to infer the ingredients from the taste and appearance. This is the essence of reverse engineering.
- Analysis of the license verification system
Inside the assembly code, they look for the function responsible for verifying the serial key.
Once they understand how to verify, they can:
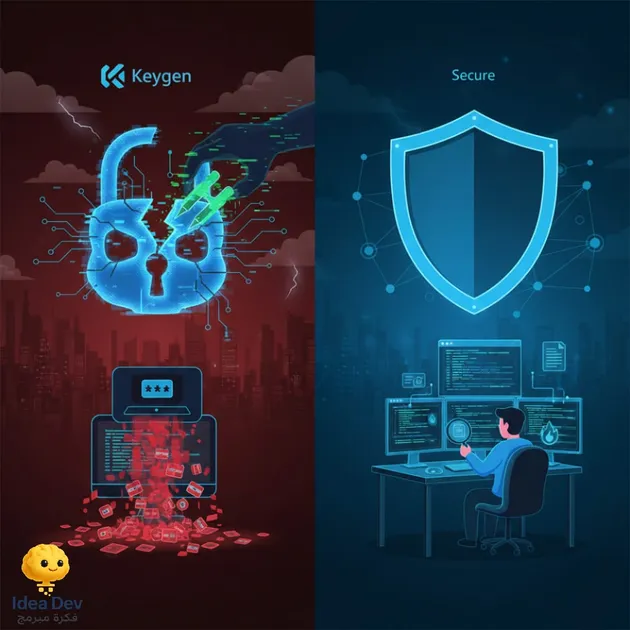
Create a program that generates valid keys (Keygen)
Or modify the program to accept any key or prevent verification completely (Patch).
👌 Why do they do that? What do they benefit from?
Pirated software may seem free... but it is often tempting bait to plant malware.
What do hackers gain?
Spreading viruses and Trojans
Steal your data and passwords
Control your device remotely (RAT)
Adding you to a botnet
You think you got a free program...but in reality you opened your door to the thief.
✌️✌️ How do they inject viruses without the original code?
It doesn't even require source code!
They can:
Modifying the executable file and injecting malicious code into it
Integrating a malicious file into a crack or keygen tool
Obfuscation code to bypass antiviruses
Create a "loader" that runs the real program and the virus together
🖐️ What are the risks to you?
Stealing passwords and bank cards
Encrypt your files and demand a ransom
Control your device stealthily
Exploiting your device to carry out electronic attacks on others
🖐️☝️️ How to protect yourself? (Ethical Security Tips)
-
Do not install any pirated software or Keygen.
-
Use free or open source alternatives (LibreOffice instead of Word, GIMP instead of Photoshop...).
-
Keep your system and security software up to date.
-
Scan any suspicious file via VirusTotal.
-
Monitor your device's performance and strange connections.
-
Use a firewall and check outgoing connections.
👏 Clear and simple summary
Crack may seem tempting... but it's actually a poisonous piece of candy. If you are interested in cybersecurity, understanding these mechanisms is necessary to use them for defense, not attack.
In The Idea of a Programmer, we teach you these concepts to protect yourselves and understand how hackers work... and this is the essence of ethical security.
#Keygen #Malware #Ethical_Hacking #Programmer_Idea #ideadev #CyberAwareness #Information_Protection